Keeping your personal information safe on your smartphone or tablet might feel like a constant battle, but it’s more manageable than you might think. Essentially, securing your mobile data boils down to a few key strategies: strong foundational security, smart app management, careful online behavior, and being prepared for the worst. By layering these approaches, you can significantly reduce your risk of data breaches and keep your sensitive details out of the wrong hands.
Think of this as putting good locks on your front door. It’s the first line of defense, and it’s surprisingly important. If someone gets physical access to your device, or if it gets lost or stolen, these basic settings are what keep your entire digital life locked down.
The Power of a Strong Lock Screen
This is your absolute first step, and frankly, if you’re not using a strong screen lock, you’re leaving a huge vulnerability open.
Passcodes vs. Patterns vs. Biometrics
- Passcodes: While a simple 4-digit PIN is better than nothing, it’s incredibly easy to guess. Aim for at least a 6-digit PIN, and consider using a combination of numbers and letters if your device allows. The longer and more random, the better.
- Patterns: These can seem intuitive, but people tend to use predictable patterns, especially if they’re drawing them on a dirty screen where the trail is visible. Avoid obvious shapes like “L” or “Z” or connecting just a few dots.
- Biometrics (Fingerprint/Face ID): These are generally seen as the most secure and convenient. They’re hard for attackers to replicate without having your physical finger or face. However, remember that even biometrics aren’t foolproof. A determined attacker might find ways to bypass them, but for everyday use, they offer excellent protection. Always have a strong backup passcode in case your fingerprint or face isn’t recognized.
Making Your Lock Screen Even Stronger
- Auto-Lock Timer: Set your device to lock automatically after a short period of inactivity, like 30 seconds or a minute. This prevents your phone from staying unlocked if you absentmindedly put it down.
- Require Passcode After Restarts: Make sure your device prompts for your passcode after it’s been turned off and on again. This is a crucial security step that some people overlook.
Encryption: Scrambling Your Data
This is like putting your most important documents in a locked safe. If your device is stolen, the data inside is gibberish to anyone who doesn’t have the key (your passcode or unlock method).
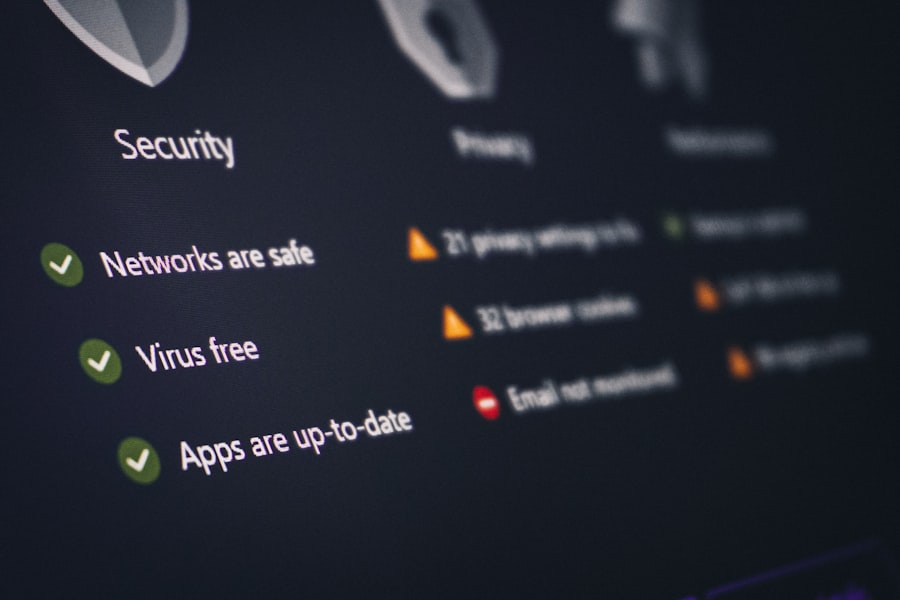
- How It Works: Encryption scrambles the data on your device, making it unreadable without the correct decryption key. Most modern smartphones have this enabled by default, but it’s worth checking.
- What to Look For: On Android, you’ll typically find this in “Security” or “Lock screen” settings. On iOS, it’s generally enabled automatically once you set a passcode.
- Always Encrypt: If your device offers encryption and it’s not on by default, turn it on immediately. It might use a tiny bit more battery, but the security trade-off is well worth it.
Keeping Your Software Up-to-Date
This is a bit like patching holes in your digital armor. Software updates often include crucial security fixes that address newly discovered vulnerabilities.
- Why Updates Matter: Companies are constantly finding and fixing security flaws. By not updating, you’re leaving those doors open for attackers.
- Automatic Updates: Enable automatic updates whenever possible. This way, you don’t have to remember to do it manually, and you’ll get the patches as soon as they’re available.
- Operating System and App Updates: Don’t just update your phone’s operating system; make sure all your individual apps are updated too. Many apps have their own security patches.
Finding Your Device: Tracking and Remote Wipe
Losing your phone is a nightmare, but having a way to locate it or wipe it clean can save your data from falling into the wrong hands.
- “Find My” Features: Both Apple (Find My iPhone) and Google (Find My Device) offer robust services that allow you to track your device’s location on a map, play a sound, lock it remotely, or even erase all data on it.
- Setting It Up: Make sure these services are enabled on your device before you lose it. They usually require you to be logged into your Apple ID or Google account.
- Remote Wipe Caution: While a powerful tool, a remote wipe is a permanent action. Use it as a last resort if you’re certain the device is unrecoverable and the data on it is highly sensitive.
In today’s digital age, securing personal data on mobile devices has become increasingly important as we rely more on our smartphones for everyday tasks. For those interested in enhancing their mobile security knowledge, a related article that provides valuable insights is available at The Ultimate Guide to the 6 Best DJ Software for Beginners in 2023. While it primarily focuses on DJ software, it also touches on the importance of protecting personal information while using various applications, making it a relevant read for anyone concerned about mobile data security.
Key Takeaways
- Clear communication is essential for effective teamwork
- Active listening is crucial for understanding team members’ perspectives
- Setting clear goals and expectations helps to keep the team focused
- Regular feedback and open communication can help address any issues early on
- Celebrating achievements and milestones can boost team morale and motivation
Navigating the App Jungle: Trustworthy Downloads and Permissions
The apps you install are gateways to your data. Being smart about which apps you download and what access you give them is paramount.
The App Store Dilemma: Stick to Official Sources
This is probably the most critical piece of advice for app security.
- Official Stores Only: Only download apps from the official Apple App Store or Google Play Store. These platforms have review processes (though not perfect) to catch malicious apps.
- Beware of Third-Party Stores and Downloads: Avoid downloading apps from unofficial websites or third-party app stores. These are breeding grounds for malware and fake apps designed to steal your information or infect your device.
- “Sideloading” Risks: While “sideloading” (installing apps from outside the official stores) can have legitimate uses for developers or power users, for the average person, it’s a significant security risk. Enable it only if you know exactly what you’re doing and trust the source explicitly.
App Permissions: What Are You Letting Them See?
Every time you install an app, it asks for permission to access certain parts of your device – your contacts, camera, location, microphone, etc. This is a key area where data can leak.
- The Principle of Least Privilege: Apps should only have access to the data and features they absolutely need to function. If a calculator app asks for access to your microphone, that’s a big red flag.
- Reviewing Permissions Regularly: Don’t just blindly accept all permissions when prompted. Take a moment to consider if the app really needs that access.
- Managing Permissions Post-Installation: You can (and should) go back and manage app permissions after they’re installed.
- On Android: Go to Settings > Apps > [App Name] > Permissions.
- On iOS: Go to Settings > Privacy, or scroll down to individual app settings.
- “While Using the App” vs. “Always”: For location, microphone, and camera permissions, opt for “While Using the App” whenever possible. This limits their access to only when you’re actively interacting with the app. “Always” should be reserved for apps that genuinely need background access (e.g., navigation apps when you’re using them for directions).
Unnecessary Apps: Less is More
Every app installed is a potential vector for attack or data leakage.
- Regular Audits: Schedule time every few months to go through your installed apps.
- Delete What You Don’t Use: If you haven’t opened an app in months, uninstall it. This reduces your attack surface and frees up storage space.
- Check for Pre-Installed Bloatware: Many devices come with pre-installed apps that you might not need. See if you can uninstall them.
Identifying Suspicious Apps
It’s not always obvious when an app is malicious.
- App Reviews and Ratings: While not foolproof, check what other users are saying. Numerous complaints about battery drain, crashes, or strange behavior can be warning signs.
- Developer Reputation: Stick with well-known and reputable developers.
- Permissions Still Don’t Add Up: If an app’s described function doesn’t match the permissions it’s requesting, be very cautious.
Online Behavior: Habits That Protect Your Data

Your actions online are just as critical as the technical settings on your device. These are the daily habits that can either leave you vulnerable or make you much more secure.
The Dangers of Public Wi-Fi
Connecting to free Wi-Fi hotspots at coffee shops, airports, or hotels can be convenient, but often insecure.
- Unencrypted Networks: Many public Wi-Fi networks are not encrypted. This means that anyone else on the same network could potentially intercept the data you’re sending and receiving, including login credentials, emails, or messages.
- Fake Hotspots: Malicious actors can set up fake Wi-Fi hotspots that look legitimate to lure users.
Once connected, they can monitor your activity.
- What to Do:
- Avoid Sensitive Transactions: Don’t log into banking apps, make purchases, or access highly sensitive accounts when on public Wi-Fi.
- Use a VPN: A Virtual Private Network (VPN) encrypts your internet traffic, making it unreadable to anyone snooping on the network. This is especially important on public Wi-Fi.
- Turn Off Auto-Connect: Configure your device not to automatically connect to open Wi-Fi networks.
Phishing and Social Engineering: Don’t Take the Bait
These are tactics where attackers trick you into revealing information or taking actions that compromise your security.
- Recognizing Suspicious Communications: Be wary of unsolicited emails, text messages, or social media messages that ask for personal information, urge you to click on links, or create a sense of urgency.
- Verify the Source: If you receive a suspicious message, don’t click any links or download attachments. Instead, go directly to the company’s official website or contact them through a known, trusted channel to verify the request.
- Common Scams: Look out for fake alerts, requests for money (e.g., “your account is compromised, send us payment”), or offers that are too good to be true.
- Two-Factor Authentication (2FA): Turn on 2FA for all your important accounts.
This adds an extra layer of security, requiring a second confirmation (like a code from your phone or a fingerprint) in addition to your password.
Browser Security: Navigating Safely
Your web browser is a primary tool for accessing information, but it can also be a gateway for threats.
- HTTPS is Your Friend: Always look for “https://” in the website’s address bar. The “s” indicates that the connection between your browser and the website is encrypted, making it more secure.
- Be Wary of Pop-Ups: Don’t click on suspicious pop-up ads, especially those that claim you’ve won something or that your device is infected.
- Browser Extensions: While useful, some browser extensions can be used to track your activity or exploit vulnerabilities. Only install extensions from trusted sources and review their permissions.
- Clear Browsing Data: Regularly clear your browser’s cache and cookies.
This can help protect your privacy by removing traces of your online activity.
Password Management: The Unsung Hero
Weak or reused passwords are one of the biggest security vulnerabilities.
- Password Managers: Use a reputable password manager. These tools generate strong, unique passwords for all your accounts and store them securely. You only need to remember one master password.
- Unique Passwords for Every Site: Never reuse passwords across different websites.
If one site is breached, all your accounts using that same password become vulnerable.
- Strong Password Characteristics: Aim for passwords that are long (at least 12 characters), a mix of uppercase and lowercase letters, numbers, and symbols. Avoid easily guessable information like birthdays or common words.
Protecting Your Data in Transit and at Rest
Even when you’re not actively using your device, your data needs protection.
This involves securing data as it travels between your device and the internet, and ensuring it’s safe when stored locally.
Securing Your Communication
When you send and receive messages, emails, or make calls, the data can be intercepted.
- Encrypted Messaging Apps: Use messaging apps that offer end-to-end encryption, such as Signal, WhatsApp (with end-to-end encryption enabled), or Telegram (for ‘secret chats’). This means only you and the recipient can read the messages.
- Email Encryption: For highly sensitive emails, consider using encrypted email services or tools like PGP (Pretty Good Privacy), although this can be more complex for casual users.
- Be Mindful of SMS: Standard SMS messages are generally not encrypted and can be more easily intercepted.
Cloud Backups: A Double-Edged Sword
Cloud backups are fantastic for data recovery, but they also need to be secured.
- Enable Encryption on Cloud Services: Check the security settings of your cloud storage provider (e.g., Google Drive, iCloud, Dropbox). Many offer optional encryption for your stored files.
- Strong Passwords for Cloud Accounts: Your cloud accounts are prime targets. Ensure they have strong, unique passwords and 2FA enabled.
- Understand What You’re Backing Up: Be aware of what data is being backed up to the cloud. If you have highly sensitive files, consider encrypting them before uploading them, or storing them locally rather than in the cloud.
- Regularly Review Backup Settings: Ensure your backup settings are still appropriate for your current needs and security posture.
Wi-Fi Calling and Bluetooth Risks
| Metrics | Data |
|---|---|
| Number of mobile devices with encryption enabled | 75% |
| Percentage of mobile devices with remote wipe capability | 80% |
| Number of reported mobile data breaches | 100 |
| Percentage of employees trained on mobile data security | 90% |
These convenient features can also introduce vulnerabilities if not managed carefully.
- Wi-Fi Calling: While generally secure when used on your trusted home network, be cautious when using Wi-Fi calling on public networks, as the traffic can be less secure.
- Bluetooth Security:
- Turn Off When Not In Use: If you’re not actively using Bluetooth, turn it off. This reduces your device’s visibility to potential attackers.
- Limit Discoverability: Make your device “not discoverable” by others when Bluetooth is on.
- Pair Only with Trusted Devices: Only pair your device with Bluetooth devices you know and trust.
- Beware of “Bluejacking” and “Bluesnarfing”: These are older types of Bluetooth attacks where attackers send unsolicited messages or steal data. Keeping Bluetooth off and discoverability limited significantly mitigates these risks.
In today’s digital age, securing personal data on mobile devices has become increasingly important, especially for professionals who rely on technology for their daily tasks. A related article that offers valuable insights into choosing the right tools for educators is available at best laptops for teachers in 2023. This resource not only highlights the top devices but also emphasizes the significance of security features that can help protect sensitive information while on the go.
Emergency Preparedness: What to Do When Things Go Wrong
No matter how careful you are, sometimes data loss or device compromise happens. Having a plan in place can make a world of difference.
Having a Data Recovery Plan
This is about being able to get your information back if something happens.
- Regular Backups: This cannot be stressed enough. Automate your backups for both your device and any critical files stored on it. This includes photos, contacts, documents, and notes.
- Multiple Backup Locations: Don’t rely on a single backup method. Use a combination of cloud backups and local backups (e.g., to a computer or external hard drive).
- Test Your Backups: Occasionally restore a file or two from your backup to ensure it’s working correctly. A backup you can’t restore from is useless.
- Two-Factor Authentication for Everything: As mentioned before, this is crucial. If your primary password is compromised, 2FA provides a critical fallback.
Responding to a Lost or Stolen Device
Act quickly to minimize damage.
- Immediately Try to Locate It: Use your “Find My” service to see if you can track it.
- Remotely Lock or Wipe: If you can’t recover it, use the “Find My” service to remotely lock the device with a new passcode or, as a last resort, erase all data.
- Change Passwords: As soon as you suspect your device is lost or stolen, change the passwords for all your important accounts, especially your email, banking, and social media. Start with the account linked to your device’s security (Google Account or Apple ID).
- Inform Your Service Provider: Contact your mobile carrier to report the phone lost or stolen. They can often block the SIM card and prevent unauthorized calls or data usage.
- Report to Authorities: If you believe your device was stolen, file a police report. This might be necessary for insurance claims and can sometimes help in recovery efforts.
Dealing with a Security Breach
If you suspect your data has been compromised.
- Identify the Breach: Try to understand how your data was compromised. Was it a specific app? A phishing email? A website you visited?
- Change Compromised Passwords Immediately: Focus on the accounts directly affected by the breach.
- Monitor Your Accounts: Keep a close eye on your bank statements, credit reports, and other financial accounts for any suspicious activity.
- Consider Identity Theft Protection: If the breach involved sensitive personal information (like Social Security numbers or driver’s license details), you might want to consider professional identity theft protection services.
- Learn from the Experience: Use the incident as a learning opportunity to reinforce your security practices.
Securing your personal data on mobile devices isn’t about achieving perfect invincibility, but about building robust layers of defense through informed habits and smart settings. By consistently applying these principles, you can significantly reduce your risk and enjoy the convenience of your mobile devices with greater peace of mind.
FAQs
What are the best practices for securing personal data on mobile devices?
Some best practices for securing personal data on mobile devices include using strong passwords or biometric authentication, enabling device encryption, keeping software and apps updated, using a VPN when connecting to public Wi-Fi, and being cautious about the apps and websites you interact with.
What is device encryption and how does it help secure personal data?
Device encryption is the process of encoding data on a device in such a way that it can only be accessed with a decryption key. This helps secure personal data by making it unreadable to unauthorized users, even if the device is lost or stolen.
How can users protect their personal data when using public Wi-Fi on their mobile devices?
Users can protect their personal data when using public Wi-Fi on their mobile devices by using a virtual private network (VPN) to encrypt their internet connection, avoiding sensitive transactions or activities, and ensuring that the websites they visit are secure (using HTTPS).
What are the risks of not securing personal data on mobile devices?
The risks of not securing personal data on mobile devices include unauthorized access to sensitive information, identity theft, financial fraud, and potential damage to personal and professional reputations.
How can users ensure that the apps and websites they interact with are secure?
Users can ensure that the apps and websites they interact with are secure by only downloading apps from trusted sources (such as official app stores), checking for secure connections (HTTPS) when browsing websites, and being cautious about the permissions requested by apps.