Ransomware. It’s a word that strikes fear into the heart of any business owner, and for Managed Service Providers (MSPs), it’s a constant threat looming over your clients and your own operations. The good news is, you’re not powerless. Proactive, well-thought-out strategies can significantly reduce your risk and improve your chances of recovery should the worst happen. This article will dive into practical, actionable ransomware defense strategies specifically tailored for MSPs, helping you protect your clients and your reputation.
First, let’s get a clear picture of why MSPs are such attractive targets for ransomware gangs. It’s not just about hitting one company; it’s about hitting many through a single point of entry.
Supply Chain Attack Vector
Imagine a hacker gaining access to your management tools – remote monitoring and management (RMM), professional services automation (PSA), or even your internal network. With that access, they can potentially deploy ransomware across your entire client base. This is a highly efficient attack for them, and a devastating one for you. Your centralized access is both your strength and your vulnerability.
Access to Sensitive Data
MSPs often have elevated privileges to client systems, hold sensitive client data, and manage critical infrastructure. This makes your network a goldmine for attackers looking for valuable information or leverage. The bigger the impact they can make, the more likely they are to get paid.
Reputation and Trust
Your business model is built on trust. A successful ransomware attack on your clients, stemming from your systems, can shatter that trust and lead to irreparable damage to your brand and customer churn. Proactive defense isn’t just about technical safeguards; it’s about safeguarding your entire business.
In the ever-evolving landscape of cybersecurity, Managed Service Providers (MSPs) must stay informed about effective Ransomware Defense Strategies to protect their clients. A related article that offers insights into the best tools for enhancing online security can be found at The Best Apps for Facebook 2023. While primarily focused on social media applications, it highlights essential security measures that can be beneficial for MSPs looking to bolster their defenses against ransomware attacks.
Key Takeaways
- Clear communication is essential for effective teamwork
- Active listening is crucial for understanding team members’ perspectives
- Setting clear goals and expectations helps to keep the team focused
- Regular feedback and open communication can help address any issues early on
- Celebrating achievements and milestones can boost team morale and motivation
Building a Strong Foundation: Core Security Principles
Before we dive into specific tools and tactics, let’s touch on the foundational principles that underpin all effective cybersecurity. These aren’t flashy, but they are absolutely essential.
Deep Dive into Network Segmentation
Think of your network like a building. Would you have one massive room where everyone has access to everything? Hopefully not. Network segmentation is about creating different “rooms” with locked doors. If an attacker breaches one segment (say, your guest Wi-Fi), they shouldn’t automatically have access to your critical production servers. This limits their lateral movement and reduces the blast radius of an attack.
- VLANs (Virtual Local Area Networks): Use VLANs to separate different types of traffic and devices. For instance, put all IoT devices on their own VLAN, administrative workstations on another, and critical servers on yet another.
- Firewall Rules: Implement strict firewall rules between segments. Only allow necessary traffic to flow between them. If your finance server doesn’t need to talk to the marketing printer, block that communication.
- Zero Trust Principles: Adopt a “never trust, always verify” approach. Even if a device is on your network, it shouldn’t automatically be granted access to resources. Every request for access should be authenticated and authorized.
Immutable Backups and Disaster Recovery Planning
Backups are your last line of defense. But just having backups isn’t enough; they need to be immune to ransomware.
- Offsite, Offline, Air-Gapped: The “3-2-1 rule” is a good start (3 copies of data, on 2 different media, 1 offsite). However, for ransomware, aim for an “air-gapped” copy. This means a backup that is physically or logically disconnected from your network, so ransomware can’t reach and encrypt it. Tapes, rotating external drives, or specific immutable cloud storage solutions are good candidates.
- Immutable Storage: Look for backup solutions that offer immutable storage, meaning once data is written, it cannot be altered or deleted for a specified period. This prevents ransomware from encrypting or deleting your backup files.
- Regular Testing and Verification: A backup that hasn’t been tested is as good as no backup at all. Regularly perform full restore tests to ensure your backup process works and that the data is intact and recoverable. Don’t wait for a disaster to find out your backups are corrupted.
- Disaster Recovery Playbook: Have a clear, documented plan for what to do when an incident occurs. Who does what? What’s the communication plan? How long should recovery take? This isn’t just about restoring data; it’s about full business continuity.
Proactive Security Measures: Layering Your Defenses

A single security solution is never enough. Think of it like an onion, with multiple layers of protection. Each layer makes it harder for an attacker to reach their goal.
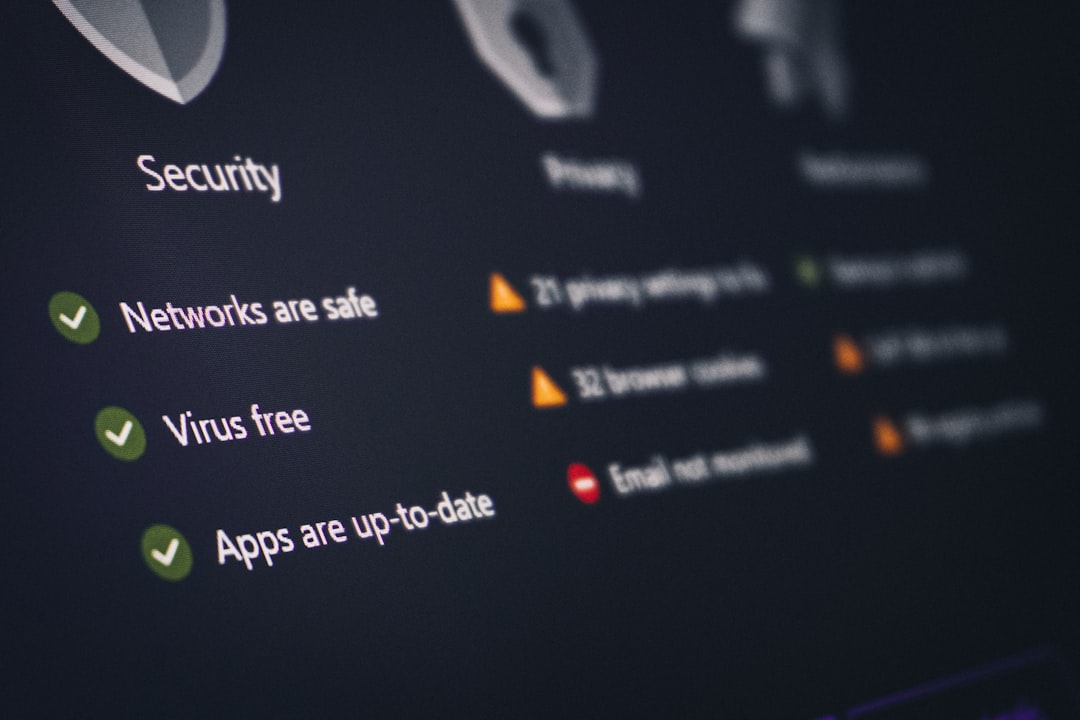
Robust Endpoint Detection and Response (EDR)
Antivirus is dead; long live EDR.
Traditional antivirus relies on known signatures, which means it’s always playing catch-up. EDR solutions go much further.
- Behavioral Analysis: EDR monitors endpoint activity for suspicious behaviors, not just known malware signatures. This allows it to detect novel and sophisticated threats that traditional AV might miss.
- Threat Hunting Capabilities: EDR provides visibility into what’s happening on your endpoints, allowing you to proactively hunt for threats that might have bypassed initial defenses.
- Automated Response: Many EDR platforms can automatically isolate compromised endpoints, terminate malicious processes, and roll back changes, limiting the damage of an attack.
- Managed Detection and Response (MDR): For MSPs, particularly those with smaller internal security teams, partnering with an MDR provider who monitors your EDR alerts 24/7 can be a game-changer.
They act as your extended security operations center (SOC).
Advanced Email Security and Awareness Training
Email remains the number one vector for ransomware delivery, typically through phishing.
- Gateway Protection: Implement advanced email filtering solutions that can detect and block malicious attachments, phishing links, and spoofed emails before they even reach an inbox. Look for features like sandboxing, where suspicious attachments are opened in a safe environment to check for malicious behavior.
- DMARC, DKIM, SPF: Ensure your own email domains (and your clients’ domains) are properly configured with DMARC, DKIM, and SPF records. These protocols help prevent email spoofing and increase the trustworthiness of legitimate emails.
- Regular Phishing Simulations: Don’t just tell users about phishing; show them.
Conduct regular, realistic phishing simulations. Those who fall for the simulations should receive immediate, targeted training to reinforce best practices.
- Security Awareness Training (Ongoing): This isn’t a one-and-done annual webinar. Security awareness should be an ongoing culture. Short, frequent modules, real-world examples, and clear communication about current threats are far more effective.
Teach users to spot red flags: suspicious senders, urgent pleas, grammatical errors, and unusual links.
Multi-Factor Authentication (MFA) Everywhere
MFA is one of the single most effective security controls against credential theft. If an attacker gets a username and password, MFA stops them in their tracks.
- Mandatory for All Access: Implement MFA for every possible service and system: RMM, PSA, VPN, all cloud services (Microsoft 365, Google Workspace, AWS, Azure), internal servers, network devices, and even client-facing portals.
- Strong MFA Methods: Prioritize strong MFA methods like FIDO2 security keys, authenticator apps (e.g., Microsoft Authenticator, Google Authenticator), or hardware tokens. Avoid SMS-based MFA where possible, as it’s more susceptible to SIM swapping attacks.
- Educate Users on MFA Prompts: Teach users to be wary of unexpected MFA prompts.
If they didn’t initiate a login, they should never approve an MFA request.
Hardening Your MSP Tools and Infrastructure
Your MSP tools are powerful, and in the wrong hands, they become powerful weapons against you. Securing them is crucial.
RMM/PSA Security Best Practices
These tools are the crown jewels for an attacker. Treat them as such.
- Least Privilege Access: Ensure technicians only have the permissions they absolutely need to do their job, and nothing more. Regularly review and audit these permissions. If a junior tech only needs to reboot a workstation, they don’t need full administrative access to every server.
- Dedicated Admin Accounts: Never use the same account for daily tasks and administrative duties. Have separate, non-privileged accounts for routine work and highly privileged accounts for administrative actions.
- IP Whitelisting & Geo-Fencing: Restrict access to your RMM/PSA to specific IP addresses (e.g., your office IPs, approved VPN gateways). If your team doesn’t operate from certain geographic regions, block access from those regions.
- Regular Audits and Review: Regularly audit successful and failed logins, configuration changes, and script executions within your RMM/PSA. Look for anomalies.
- Patching and Updating: Keep your RMM/PSA software, including any on-premise components, fully patched and up-to-date. Vendors frequently release security updates – apply them promptly.
Network and Server Hardening
This is about making your internal environment as resistant to attack as possible.
- Patch Management Automation: Implement robust patch management for all operating systems, applications, and firmware across your internal infrastructure and your clients’. Automated patching with proper testing is key.
- Vulnerability Management: Regularly scan your networks and systems for vulnerabilities. Prioritize and remediate findings based on risk. A vulnerability scanner can highlight misconfigurations or outdated software that attackers exploit.
- Intrusion Detection/Prevention Systems (IDS/IPS): Deploy IDS/IPS at network perimeter and key internal choke points. These systems monitor network traffic for malicious activity and can block attacks in real-time.
- Principle of Least Functionality: Disable any unnecessary services, ports, or protocols on servers and network devices. The less surface area an attacker has to explore, the better.
In the ever-evolving landscape of cybersecurity, Managed Service Providers (MSPs) must stay informed about the latest threats and defense strategies, particularly concerning ransomware. A related article that discusses emerging trends in social media, including Instagram, can provide insights into how cybercriminals exploit these platforms for phishing attacks and other malicious activities. Understanding these trends is crucial for MSPs looking to enhance their ransomware defense strategies. For more information, you can read the article on top trends on Instagram in 2023.
Incident Response Planning: When the Worst Happens
| Defense Strategy | Description |
|---|---|
| Regular Data Backups | Implementing regular backups of critical data to ensure quick recovery in case of a ransomware attack. |
| Employee Training | Providing comprehensive training to employees on how to identify and avoid potential ransomware threats. |
| Network Segmentation | Dividing the network into smaller segments to contain the spread of ransomware in case of an attack. |
| Endpoint Security | Deploying advanced endpoint security solutions to detect and prevent ransomware attacks on devices. |
| Incident Response Plan | Developing a detailed plan to respond to and recover from ransomware incidents effectively. |
No matter how many defenses you put in place, the possibility of a breach remains. A well-rehearsed plan can mean the difference between a minor incident and a catastrophic failure.
Develop a Comprehensive Incident Response Plan (IRP)
Your IRP should be a living document, detailing specific steps for various incident types, especially ransomware.
- Clear Roles and Responsibilities: Who is the incident commander? Who handles communications? Who does technical remediation? Everyone needs to know their role.
- Detection and Containment: How will you detect ransomware? What are the immediate steps to contain it (e.g., isolating affected systems, disconnecting from the network)? The faster you contain, the less damage is done.
- Eradication and Recovery: Detailed steps for removing the ransomware, restoring data from backups, and bringing systems back online. This should align with your disaster recovery plan.
- Post-Incident Analysis: What went wrong? How can we prevent it from happening again? This involves reviewing logs, identifying the root cause, and updating your defenses.
- Communication Plan: Who needs to be informed? Clients, legal counsel, insurance providers, regulatory bodies? What will you say, and when? Transparency, balanced with caution, is crucial.
Regular Drills and Testing
An IRP that sits on a shelf is useless. You need to practice it.
- Tabletop Exercises: Regular “what-if” scenarios where your team walks through the plan, identifies gaps, and refines processes. These don’t involve actual system disruption but are critical for alignment.
- Simulated Incidents: Periodically conduct more realistic simulations, perhaps involving a test environment, to gauge your team’s actual response time and effectiveness.
- Update the Plan: Every drill or real incident will reveal areas for improvement. Continuously update your IRP based on lessons learned.
Engage with Legal and Cyber Insurance
These are your lifelines if an attack bypasses your technical controls.
- Cyber Insurance Review: Understand your policy’s coverage before an incident. What are the notification requirements? Does it cover ransom payments (though paying is generally discouraged)? Does it cover business interruption?
- Legal Counsel: Have an attorney specializing in cybersecurity and data privacy on retainer. They can guide you through legal obligations, regulatory reporting, and negotiations if necessary. Don’t wait until you’re in crisis mode to find one.
In the ever-evolving landscape of cybersecurity, Managed Service Providers (MSPs) must stay informed about the latest threats and defenses, particularly regarding ransomware. A comprehensive understanding of effective ransomware defense strategies is crucial for MSPs to protect their clients’ data and maintain trust. For those looking to enhance their knowledge on related topics, an insightful article on the best laptops for coding and programming can provide valuable information on the tools that cybersecurity professionals should consider.
You can read more about it
5G Innovations (13) Wireless Communication Trends (13) Article (343) Augmented Reality & Virtual Reality (730)
- Metaverse (182)
- Virtual Workplaces (35)
- VR & AR Games (34)
Cybersecurity & Tech Ethics (718)
- Cyber Threats & Solutions (3)
- Ethics in AI (33)
- Privacy Protection (32)
Drones, Robotics & Automation (400)
- Automation in Industry (33)
- Consumer Drones (33)
- Industrial Robotics (33)
EdTech & Educational Innovations (258)
- EdTech Tools (18)
- Online Learning Platforms (4)
- Virtual Classrooms (34)
Emerging Technologies (1,553) FinTech & Digital Finance (361) Frontpage Article (1) Gaming & Interactive Entertainment (295) Health & Biotech Innovations (545)
- AI in Healthcare (3)
- Biotech Trends (4)
- Wearable Health Devices (421)
News (97) Reviews (129) Smart Home & IoT (364)
- Connected Devices (3)
- Home Automation (4)
- Robotics for Home (33)
- SmartPhone (48)
Space & Aerospace Technologies (258)
- Aerospace Innovations (4)
- Commercial Spaceflight (3)
- Space Exploration (62)
Sustainable Technology (613) Tech Careers & Jobs (253) Tech Guides & Tutorials (887)
- DIY Tech Projects (3)
- Getting Started with Tech (60)
- Laptop & PC (58)
- Productivity & Everyday Tech Tips (237)
- Social Media (64)
- Software (234)
- Software How-to (3)
Uncategorized (146)