Zero Trust for your internal applications means treating every access request, even from inside your network, as if it comes from an untrusted source. Instead of assuming trust once someone is “in,” you continuously verify their identity and the device they’re using, and you only grant them the bare minimum access needed for their current task. It’s a fundamental shift from the old “trust but verify” to “never trust, always verify.”
Why Bother with Zero Trust?
You might be thinking, “My internal network is secure, why go through all this trouble?” Well, the reality is that traditional perimeter-based security isn’t enough anymore.
Insider threats, compromised credentials, and sophisticated phishing attacks can all bypass your external firewalls.
Once an attacker is inside, they often have free rein. Zero Trust aims to stop that lateral movement dead in its tracks. It’s about making your internal applications much harder for attackers to exploit, even if they manage to get their foot in the door.
Before we dive into the how-to, let’s make sure we’re all on the same page about what Zero Trust truly means in practice. It’s not just a product you buy; it’s a strategic approach to security.
Old Guard vs. New Guard: Perimeter vs. Zero Trust
Think of it like this: traditional security is a big castle with a moat and high walls. Once you’re inside the castle walls, you’re generally free to roam around. Zero Trust, however, is more like every single room in the castle having its own heavily guarded checkpoint. You need to prove who you are and why you need access to that specific room every single time you want to enter.
Core Principles in Action
- Never Trust, Always Verify: This is the mantra. No user, device, or application is inherently trusted.
- Least Privilege Access: Grant only the access absolutely necessary for a user to perform their task, and for the shortest possible time.
- Assume Breach: Operate under the assumption that your network has already been compromised. This mindset helps you build defenses that are robust even in a worst-case scenario.
- Microsegmentation: Break your network into tiny, isolated segments, limiting lateral movement if one segment is breached.
- Multi-Factor Authentication (MFA) Everywhere: MFA should be non-negotiable for every internal application access, not just for external logins.
In the context of enhancing security measures for internal applications, the concept of Zero Trust Access has gained significant traction. For those interested in exploring the latest technology trends that can complement such security frameworks, a related article on the best Huawei laptops of 2023 can provide valuable insights. These devices are known for their robust performance and security features, making them suitable for organizations looking to implement Zero Trust principles effectively. To learn more about these laptops, you can read the article here: The Best Huawei Laptop 2023.
Key Takeaways
- Clear communication is essential for effective teamwork
- Active listening is crucial for understanding team members’ perspectives
- Setting clear goals and expectations helps to keep the team focused
- Regular feedback and open communication can help address any issues early on
- Celebrating achievements and milestones can boost team morale and motivation
Key Components of a Zero Trust Architecture for Internal Apps
Implementing Zero Trust isn’t about flipping a switch. It involves integrating several technologies and changing some long-standing practices.
Identity and Access Management (IAM)
Your IAM solution is the bedrock of Zero Trust. Without robust identity verification, the whole concept falls apart.
- Strong Authentication (MFA/SSO): Every user attempting to access an internal application must undergo strong authentication. This typically means multi-factor authentication (MFA) at a minimum. Single Sign-On (SSO) can help streamline the user experience while maintaining strong authentication at the initial login. This isn’t just about passwords; it’s about biometrics, token-based systems, and other advanced methods.
- Centralized User Directories: Active Directory, LDAP, Okta, Azure AD – you need a single source of truth for user identities and their associated attributes (roles, departments, etc.). This ensures consistent policy enforcement.
- Role-Based Access Control (RBAC): Define clear roles within your organization and assign access permissions based on those roles. This simplifies management and helps enforce least privilege. Don’t grant access directly to users; grant it to roles, and then assign users to those roles.
Device Trust and Posture Management
It’s not just about who is accessing, but what they’re using to access your applications. A compromised device is a huge risk, even if the user is legitimate.
- Endpoint Detection and Response (EDR): EDR solutions provide continuous monitoring and analysis of endpoint activity. They can detect anomalies, malware, and suspicious behavior, which is crucial for assessing device health.
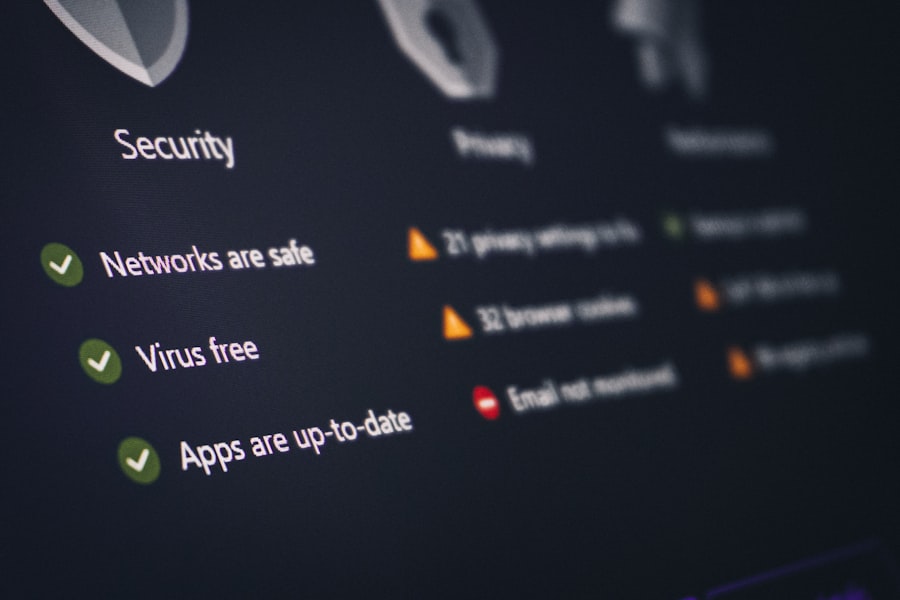
- Device Health Checks: Before granting access, your system should check the device’s security posture. Is the operating system up-to-date? Is the antivirus running and current? Is the firewall enabled? Is it encrypted? Devices that don’t meet minimum security standards should be quarantined or denied access.
- Conditional Access Policies: Combine user identity, location, device health, and application sensitivity to create dynamic access policies. For example, a user might get full access from a corporate-managed laptop on the office network, but only read-only access from an unmanaged personal device outside the office.
Microsegmentation and Network Visibility
This is where you break down your flat internal network into smaller, more manageable, and more secure segments.
- Application Segmentation: Instead of lumping all your servers into one “server farm,” segment them based on the applications they host. For example, your HR application servers should be in a different segment than your finance application servers.
- User Segmentation: Similarly, segment users based on their roles. A developer segment should be kept separate from an HR segment, even if they’re in the same physical office.
- Traffic Monitoring and Analysis: You need to see what’s happening on your network. Implement tools that can inspect and log all traffic between segments. This helps detect anomalous behavior, potential breaches, and ensures policies are being enforced correctly. Think of it as always having a security guard watching the doors between your castle rooms.
Policy Enforcement Point (PEP) / Access Proxy
This is the “gatekeeper” that sits in front of your applications and makes the real-time access decisions.
- API Gateways: For microservices-based applications, an API gateway can act as a PEP, enforcing policies before requests even reach the application logic.
- Proxy Servers: A reverse proxy can sit in front of traditional web applications, inspecting incoming requests and enforcing access policies before forwarding them to the application server.
- Software-Defined Perimeter (SDP): Also known as Zero Trust Network Access (ZTNA), SDP solutions create a secure, authenticated, and encrypted tunnel to only the specific applications a user is authorized to access, effectively making the applications invisible to unauthorized users. This dynamic perimeter makes lateral movement extremely difficult.
A Step-by-Step Approach to Implementation

Don’t try to tackle everything at once. Zero Trust is a journey, not a destination. Start small, learn, and expand.
1.
Identify Your Crown Jewels
You can’t protect everything equally from day one. Figure out what’s most critical to your business – sensitive data, critical applications, intellectual property. These are your priority targets for Zero Trust implementation.
- Data Classification Exercise: Categorize your data based on its sensitivity (e.g., public, internal, confidential, highly restricted).
This informs your access policies.
- Application Inventory: List all your internal applications. For each, identify its purpose, the data it handles, and who uses it. Understand its dependencies.
2.
Map Existing Data Flows and Access Patterns
You need to understand how users currently interact with your applications. This helps you identify gaps and unnecessary access.
- Network Traffic Analysis: Use network monitoring tools to observe actual traffic patterns. Who is talking to what, and on what ports?
This will highlight unauthorized communication or excessive access.
- User Behavior Analytics (UBA): UBA tools can help identify baseline user behavior and flag deviations that might indicate a compromise or policy violation.
3. Implement Stronger Identity and Access Management
This is often the lowest hanging fruit and provides significant security improvements quickly.
- Mandate MFA for ALL Internal Applications: No exceptions. Start with your most critical applications and then roll it out everywhere.
- Review and Revise RBAC Policies: Are your roles still relevant?
Are users assigned to the correct roles? Are there any “super-user” accounts that need to be reined in? Regularly audit user permissions.
- Centralize User Identities: If you have disparate identity stores, work towards consolidating them into one authoritative source.
4.
Segment Your Network and Applications
This is a more complex step but crucial for limiting lateral movement.
- Start with Virtual Segmentation: Use VLANs and firewall rules to create initial logical segments for your most critical applications.
- Progress to Microsegmentation: Deploy specialized tools that can define and enforce policies at a more granular, application-level. This is where you can say, “Only Bob on his corporate laptop can access the HR database from this specific IP range.”
- Implement an Access Proxy/ZTNA for Key Applications: Instead of opening up network segments to everyone, use ZTNA to grant access only to authorized users and devices for specific applications. This makes the applications “dark” to anyone else.
5.
Continuously Monitor and Adapt
Zero Trust isn’t a set-it-and-forget-it solution. The threat landscape, your applications, and your business needs will evolve.
- Logging and Auditing: Log every access attempt, every policy decision, and every change. This provides an audit trail for forensics and compliance.
- Security Information and Event Management (SIEM): Aggregate your logs into a SIEM for centralized analysis, correlation, and alerting on suspicious activities.
- Scheduled Access Reviews: Periodically review user access permissions to ensure they are still appropriate.
Remove access for users who no longer need it (e.g., job changes, departures).
- Regular Policy Audits: Review your Zero Trust policies frequently. Are they still effective? Are there any loopholes?
Do they align with your business requirements?
- Threat Intelligence Integration: Integrate threat intelligence feeds into your security tools to help identify and block known malicious IPs, domains, and attack patterns.
6. Educate Your Team
Your technology is only as good as the people using it.
- User Training: Explain to your employees why Zero Trust is being implemented and how it benefits them (e.g., protecting their data and job security). Teach them about MFA, phishing awareness, and device hygiene.
- IT/Security Team Training: Ensure your security and IT operations teams are fully trained on the new tools and processes.
They need to understand the underlying principles and how to troubleshoot issues.
Common Challenges and How to Overcome Them
Implementing Zero Trust isn’t without its bumps in the road. Being aware of them can help you prepare.
Legacy Applications
Many internal applications are old, difficult to modify, and might not natively support modern authentication or network policies.
- Solution: Use proxies or API gateways. Place an access proxy or API gateway in front of legacy applications. This allows you to enforce authentication, authorization, and posture checks before the request even reaches the application, without modifying the application itself.
- Solution: Application refactoring (long-term). As older applications are replaced or updated, ensure that new development incorporates Zero Trust principles from the start.
Too Much Friction for Users
| Metrics | Value |
|---|---|
| Number of internal applications | 50 |
| Number of users accessing internal applications | 1000 |
| Implementation cost | 50,000 |
| Time to implement Zero Trust Access | 6 months |
Adding security steps can sometimes make things harder for legitimate users, leading to frustration and workarounds.
- Solution: Balance security with usability. Use SSO where possible, provide clear communication about why these steps are necessary, and ensure strong user support.
- Solution: Conditional access. Implement policies that grant more seamless access from trusted devices and locations, while requiring more stringent checks for less trusted scenarios. For example, a user on their corporate laptop in the office might have a simpler experience than a contractor using a personal device from a coffee shop.
Complexity and Management Overhead
Zero Trust can involve many different tools and a lot of policy management.
- Solution: Phased implementation. Don’t try to boil the ocean. Start with your most critical assets and expand gradually.
- Solution: Automation. Automate policy enforcement, user provisioning/deprovisioning, and device posture checks as much as possible to reduce manual overhead. Leverage orchestration tools.
- Solution: Look for integrated solutions. Some vendors offer suites that integrate IAM, ZTNA, and security posture management, which can simplify deployment and management.
Cost
Zero Trust can involve investments in new tools and professional services.
- Solution: Justify with risk reduction. Frame the cost not as an expense, but as an investment in reducing business risk, protecting intellectual property, and avoiding costly breaches.
- Solution: Leverage existing investments. See where your current security tools (firewalls, EDR, IAM) can be extended or adapted to fit into a Zero Trust framework before buying entirely new solutions.
In the realm of cybersecurity, the concept of Zero Trust Access has gained significant traction, particularly for safeguarding internal applications. A related article that delves into this topic can be found here, where it explores the intricacies of implementing such a framework effectively. By adopting a Zero Trust model, organizations can enhance their security posture and ensure that access is granted based on strict verification processes rather than assumed trust. This approach is crucial in today’s digital landscape, where threats are constantly evolving and traditional security measures may no longer suffice. For further insights, you can read more about the implications of this strategy in the linked article.
The Future of Internal Application Security
Zero Trust isn’t a fad; it’s becoming the gold standard for securing modern enterprises. As more applications move to the cloud, as remote work becomes standard, and as the threat landscape continues to evolve, the traditional perimeter simply won’t cut it. By embracing a “never trust, always verify” mindset for your internal applications, you’re not just reacting to threats; you’re proactively building a more resilient and secure organization. It’s about protecting your critical assets, ensuring business continuity, and giving your employees secure and efficient access to the tools they need to do their jobs.
FAQs
What is Zero Trust Access?
Zero Trust Access is a security model that requires strict identity verification for every person and device trying to access resources on a private network, regardless of whether they are sitting within or outside of the network perimeter.
Why is Zero Trust Access important for internal applications?
Zero Trust Access is important for internal applications because it helps prevent unauthorized access and lateral movement within the network. It ensures that only authorized users and devices can access specific resources, reducing the risk of data breaches and insider threats.
How can Zero Trust Access be implemented for internal applications?
Zero Trust Access for internal applications can be implemented by using technologies such as multi-factor authentication, micro-segmentation, and continuous monitoring. Access controls and policies should be enforced at the application level, and all traffic should be inspected for potential threats.
What are the benefits of implementing Zero Trust Access for internal applications?
The benefits of implementing Zero Trust Access for internal applications include improved security posture, reduced risk of data breaches, better visibility and control over network traffic, and the ability to enforce least privilege access.
What are some best practices for implementing Zero Trust Access for internal applications?
Some best practices for implementing Zero Trust Access for internal applications include conducting thorough risk assessments, defining access policies based on the principle of least privilege, regularly monitoring and auditing access controls, and educating employees about the importance of Zero Trust security measures.

