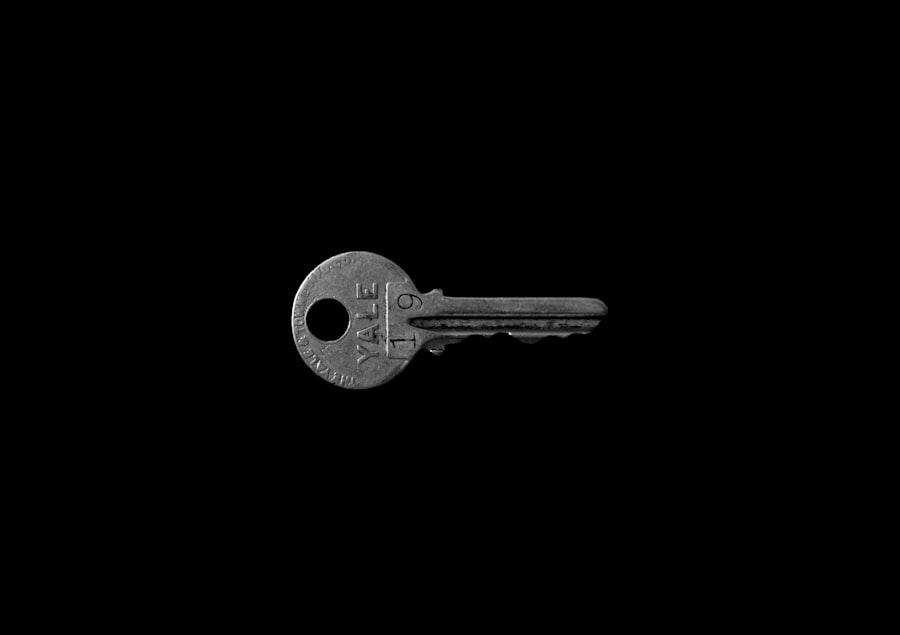
Cryptographic key management is the secure and efficient administration of cryptographic keys throughout their lifecycle. This encompasses generation, storage, distribution, usage, and destruction. In essence, it defines how an organization handles the digital secrets that protect its information. Without robust key management, the strongest encryption algorithms are rendered ineffective. Consider cryptographic keys as the physical keys to a vault containing valuable assets; if those keys are lost, stolen, or mishandled, the vault’s security is compromised, regardless of its strength.
The lifecycle of a cryptographic key involves several distinct stages, each requiring specific procedures and controls to maintain security. Mismanagement at any stage can undermine the entire cryptographic system.
Key Generation
The process of creating cryptographic keys is fundamental to their security. Keys must be statistically random and of sufficient length to resist brute-force attacks.
- Randomness: Keys must be generated using cryptographically secure pseudorandom number generators (CSPRNGs) or true random number generators (TRNGs). Predictable keys are easily guessed, compromising encrypted data.
- Length: The length of a key directly correlates with its resistance to computational attacks. Longer keys provide a larger key space, making exhaustive search infeasible within a practical timeframe. For symmetric keys, common lengths include 128, 192, and 256 bits. For asymmetric keys, lengths like 2048 or 4096 bits are standard.
- Key Derivation: In some cases, keys are derived from other secret information, such as passwords or master keys, using key derivation functions (KDFs). This adds a layer of complexity and should be implemented carefully to avoid vulnerabilities.
Key Storage
Once generated, keys require secure storage to prevent unauthorized access. This is akin to safeguarding the actual physical key to a secure area.
- Hardware Security Modules (HSMs): HSMs are dedicated physical devices designed to securely store and manage cryptographic keys. They provide a tamper-resistant environment for key operations, preventing keys from being extracted.
- Key Management Systems (KMS): A KMS is a comprehensive system that manages the full lifecycle of cryptographic keys, often employing HSMs for secure storage.
- Software Key Stores: While less secure than hardware-based solutions, software key stores encrypt keys at rest. Their security depends on the underlying operating system and application security.
- Separation of Duties: It is critical to implement separation of duties, ensuring no single individual has complete control over all aspects of key storage and access.
Key Distribution and Exchange
Sharing cryptographic keys, particularly symmetric keys, is a critical and sensitive operation. If keys are compromised during distribution, all subsequent encrypted communications are at risk.
- Asymmetric Cryptography for Key Exchange: Public-key cryptography, such as RSA or Elliptic Curve Diffie-Hellman (ECDH), is frequently used to securely exchange symmetric keys. The public key is used to encrypt the symmetric key, which can only be decrypted by the corresponding private key. This method avoids the need for a pre-shared secret for key exchange.
- Secure Channels: When direct exchange is necessary, a previously established secure channel (e.g., using a secure VPN or an out-of-band mechanism) should be employed to transmit keys.
- Key Wrapping: Encrypting a key with another key (a “key-encrypting key”) before distribution is known as key wrapping. This adds a layer of protection during transit.
Key Usage
Keys are designed for specific purposes, such as encryption, decryption, digital signatures, or authentication. Their usage must be governed by strict policies.
- Purpose Restrictions: Keys should be designated for a specific cryptographic purpose and not repurposed. For instance, a key used for encryption should not also be used for digital signing.
- Access Control: Only authorized applications or users should have access to keys for their designated operations. Access controls should be granular and enforced at the system level.
- Key Rotation: Regularly changing keys (key rotation) minimizes the impact of a compromised key. If a key is compromised, only data encrypted with that specific key is at risk, limiting the exposure.
In the realm of cybersecurity, understanding cryptographic key management is essential for safeguarding sensitive information. A related article that explores the innovative features of modern technology, such as the Samsung Galaxy Chromebook 4, highlights how advancements in devices can enhance security measures. You can read more about this in the article on the new world of possibilities with the Samsung Galaxy Chromebook 4. As organizations increasingly rely on digital solutions, effective key management practices become critical in protecting data integrity and confidentiality.
Key Revocation and Destruction
When a key is no longer needed, or if its security is compromised, it must be revoked and securely destroyed. This is like disposing of a physical key that has been lost or stolen.
- Revocation: Revocation renders a key unusable before its scheduled expiry date. This is crucial if a key is suspected of being compromised. For public keys, Certificate Revocation Lists (CRLs) or Online Certificate Status Protocol (OCSP) are used.
- Secure Destruction: Simply deleting a key file may not be sufficient. Keys must be cryptographically erased (overwritten multiple times) or physically destroyed if stored on hardware modules to prevent recovery.
- Archival: In some cases, keys used for long-term data encryption may need to be securely archived even after their active use, for legal or compliance reasons. This requires specific secure archival practices.
In the realm of digital security, understanding cryptographic key management is essential for safeguarding sensitive information. For those interested in exploring related topics, you might find it beneficial to read the article on how to choose your child’s first tablet. This article provides insights into ensuring that the devices we give to our children are secure and well-managed, which parallels the importance of managing cryptographic keys effectively. You can read more about it here: How to Choose Your Child’s First Tablet.
Why Cryptographic Key Management is Critical
The importance of robust cryptographic key management cannot be overstated. It forms the bedrock of secure data practices.
Data Confidentiality
The primary goal of encryption is to maintain data confidentiality, ensuring that only authorized individuals can access sensitive information. Effective key management is central to this.
- Preventing Unauthorized Decryption: If keys are compromised, any data encrypted with those keys becomes accessible to unauthorized parties, entirely nullifying the protection encryption was meant to provide.
- Meeting Regulatory Requirements: Many data protection regulations (e.g., GDPR, HIPAA, PCI DSS) mandate strong encryption and, by extension, secure key management practices to protect personal and financial data. Failure to comply can result in severe financial penalties and reputational damage.
Data Integrity
Beyond confidentiality, cryptographic processes also ensure data integrity, meaning data has not been altered or tampered with.
- Digital Signatures: Keys are used to create digital signatures, which provide assurance that a message or document originated from the claimed sender and has not been modified in transit. If the signing key is compromised, forged signatures can be created, leading to trust erosion.
- Message Authentication Codes (MACs): MACs use symmetric keys to verify data integrity and authenticity. A compromised MAC key allows for the creation of fraudulent messages that appear authentic.
Non-Repudiation
Non-repudiation ensures that an entity cannot falsely deny having performed an action (e.g., sending a message or signing a document).
- Attributing Actions: Cryptographic keys enable verifiable attribution of actions. If private keys are not securely managed, an attacker could impersonate an individual or entity, performing actions that are then falsely attributed to the legitimate owner of the key.
Operational Efficiency and Scalability
While primarily focused on security, effective key management also contributes to operational efficiency, especially in large and complex environments.
- Automated Processes: A well-implemented KMS can automate many key management tasks, reducing manual errors and freeing up security personnel for higher-level tasks. This includes automated key rotation, archival, and revocation.
- Centralized Control: Centralized key management provides a unified view and control over all cryptographic keys within an organization, simplifying auditing and policy enforcement.
- Scalability: As an organization grows and its data security needs expand, a robust KMS can scale accordingly, managing an increasing number of keys and cryptographic operations without compromising security or performance.
Risk Mitigation
Effective key management is a crucial component of an organization’s overall risk mitigation strategy. It addresses potential vulnerabilities arising from cryptographic implementations.
- Insider Threats: Secure key management, particularly the use of HSMs and separation of duties, mitigates the risk of insider threats by making it difficult for malicious insiders to access or compromise keys.
- External Attacks: By safeguarding keys, organizations significantly reduce their attack surface. Protecting keys makes it more difficult for external attackers to decrypt stolen data or impersonate legitimate users.
- Compliance and Auditing: Comprehensive key management systems provide audit trails for all key operations, demonstrating compliance with internal policies and external regulations. This transparency is vital for forensic investigations and proving adherence to security standards.
Challenges in Cryptographic Key Management
Despite its critical importance, cryptographic key management presents several complex challenges for organizations.
Complexity and Fragmentation
Modern IT environments are complex, involving diverse applications, multiple cloud providers, and various cryptographic standards. This leads to fragmented key management practices.
- Distributed Systems: Managing keys across on-premises infrastructure, multiple cloud providers (AWS, Azure, GCP), and hybrid environments introduces significant complexity. Each platform may have its own key management service, leading to silos.
- Diverse Cryptographic Needs: Different applications require different types of keys (symmetric, asymmetric), algorithms, and key lengths. Coordinating these diverse requirements securely is a substantial undertaking.
- Lack of Standardization: While some standards exist, a universal, seamless key management framework across all platforms remains elusive, forcing organizations to integrate disparate solutions.
Human Error and Insider Threat
Humans are often the weakest link in any security chain, and key management is particularly susceptible to human error or malicious intent.
- Misconfiguration: Incorrectly configuring key access controls, key usage policies, or key generation parameters can open severe vulnerabilities.
- Poor Practices: Weak passwords for key store access, storing keys in insecure locations (e.g., plain text files), or failing to revoke compromised keys are common errors.
- Insider Access: Individuals with legitimate access to key management systems or the ability to influence key handling processes pose a significant risk if they act maliciously.
Performance and Scalability
Implementing strong security measures, including comprehensive key management, can sometimes impact system performance.
- Cryptographic Overhead: Cryptographic operations, especially those involving asymmetric keys or frequent key derivations, consume computational resources.
- Latency: Secure key delivery and authorization processes can introduce latency, especially in distributed environments or high-throughput applications.
- Managing High Volumes of Keys: As data volumes grow and encryption becomes pervasive, organizations may need to manage millions or even billions of keys, presenting a significant scalability challenge for traditional systems.
Compliance and Regulatory Demands
The evolving landscape of data protection regulations places significant demands on key management practices.
- Specific Requirements: Regulations like GDPR (Europe), HIPAA (US), and PCI DSS (global for payment card data) have specific clauses related to the protection of sensitive data through encryption, indirectly requiring robust key management.
- Auditing and Reporting: Organizations must demonstrate effective key management to auditors, providing evidence of compliance, audit trails, and policy enforcement. This requires comprehensive logging and reporting capabilities.
- Cross-Border Data Flows: Managing keys for data that flows across international borders can introduce further complexity due to differing legal jurisdictions and data sovereignty requirements.
Best Practices for Cryptographic Key Management

To address these challenges, organizations should adopt a comprehensive approach to key management, guided by established best practices.
Implement a Centralized Key Management System (KMS)
| Metric | Description | Importance | Example |
|---|---|---|---|
| Key Generation | The process of creating cryptographic keys using secure algorithms. | Ensures keys are strong and unpredictable to prevent unauthorized access. | Generating a 256-bit AES key for data encryption. |
| Key Storage | Securely storing keys to prevent theft or loss. | Protects keys from being compromised, which could lead to data breaches. | Using Hardware Security Modules (HSMs) to store keys. |
| Key Distribution | Safely delivering keys to authorized users or systems. | Prevents interception or misuse of keys during transmission. | Using encrypted channels to share keys between servers. |
| Key Rotation | Regularly updating keys to limit exposure if compromised. | Reduces risk by limiting the time a key is valid. | Changing encryption keys every 90 days. |
| Key Revocation | Invalidating keys that are no longer secure or needed. | Prevents use of compromised or outdated keys. | Revoking a key after detecting suspicious activity. |
| Access Control | Restricting who can access or use cryptographic keys. | Ensures only authorized personnel can manage keys. | Implementing role-based access to key management systems. |
| Audit and Compliance | Tracking key usage and management activities. | Supports security policies and regulatory requirements. | Maintaining logs of key access and changes for audits. |
A dedicated KMS provides a unified platform for managing all cryptographic keys across the organization.
- Single Pane of Glass: Offers centralized control and visibility over the entire key lifecycle, simplifying management and auditing.
- Automation: Automates routine tasks like key generation, rotation, and revocation, reducing human error and enhancing efficiency.
- Policy Enforcement: Enables consistent enforcement of security policies across all keys and applications.
Utilize Hardware Security Modules (HSMs)
HSMs are the gold standard for secure key storage and cryptographic operations.
- Tamper Resistance: HSMs are designed to be tamper-resistant and tamper-evident, protecting keys from physical attacks.
- Secure Execution: Cryptographic operations are performed within the HSM, ensuring keys are never exposed in plaintext outside the device.
- Compliance: Many regulatory standards practically necessitate the use of HSMs for high-assurance key storage.
Enforce Strong Access Controls and Separation of Duties
Limiting who can access and manage keys is paramount.
- Principle of Least Privilege: Grant users and applications only the minimum necessary privileges required to perform their tasks.
- Multi-Factor Authentication (MFA): Require MFA for access to key management systems and critical key operations.
- Role-Based Access Control (RBAC): Define distinct roles with specific permissions for key management tasks, preventing any single individual from having excessive control.
- Quorum Approval: For highly sensitive operations (e.g., key generation for critical systems), require approval from multiple authorized individuals.
Implement Key Rotation and Revocation Procedures
Regularly changing keys and having clear procedures for their immediate invalidation are critical.
- Scheduled Rotation: Define clear policies for how often keys are rotated (e.g., annually, semi-annually).
- Emergency Revocation: Establish a clear process for immediate revocation of keys suspected of being compromised, including communication protocols and data remediation plans.
- Secure Archival (When Necessary): For keys associated with long-term data retention requirements, develop secure archival methods, including separate storage and access controls.
Conduct Regular Audits and Monitoring
Continuous oversight is essential to ensure compliance and detect potential issues.
- Audit Trails: Maintain detailed, immutable audit logs of all key management activities, including key generation, access, usage, and destruction.
- Regular Review: Periodically review logs and audit trails for anomalies, unauthorized access attempts, or policy violations.
- Penetration Testing: Include key management infrastructure in regular security assessments and penetration tests to identify vulnerabilities.
In conclusion, cryptographic key management is not merely a technical detail; it is a fundamental pillar of modern cybersecurity. It is the invisible thread that connects secure data to trusted operations. Without a deliberate, well-implemented, and continually monitored approach to key management, even the most advanced encryption becomes a facade, and sensitive data remains vulnerable. As organizations increasingly rely on encryption to protect their assets and comply with regulations, understanding and mastering cryptographic key management becomes an indispensable requirement for maintaining trust and ensuring the integrity of the digital world.
FAQs
What is cryptographic key management?
Cryptographic key management refers to the processes and mechanisms involved in generating, distributing, storing, using, and retiring cryptographic keys securely. It ensures that keys are protected throughout their lifecycle to maintain the confidentiality, integrity, and authenticity of encrypted data.
Why is cryptographic key management critical?
Effective key management is critical because the security of encrypted data depends entirely on the protection of cryptographic keys. If keys are compromised, unauthorized parties can decrypt sensitive information, leading to data breaches, loss of privacy, and potential financial and reputational damage.
What are the main components of cryptographic key management?
The main components include key generation, key distribution, key storage, key usage, key rotation or renewal, key backup, and key destruction. Each component must be carefully managed to prevent unauthorized access and ensure keys remain secure throughout their lifecycle.
How does cryptographic key management impact compliance?
Many regulatory frameworks and industry standards, such as GDPR, HIPAA, and PCI DSS, require organizations to implement strong cryptographic key management practices. Proper key management helps organizations meet these compliance requirements by safeguarding sensitive data and demonstrating control over encryption processes.
What are common challenges in cryptographic key management?
Common challenges include securely generating and distributing keys, preventing unauthorized access, managing key lifecycle events like rotation and revocation, integrating key management with existing systems, and ensuring scalability and usability without compromising security. Addressing these challenges is essential for maintaining robust encryption security.