Proof-of-Stake (PoS) has come a long way, and its evolution has profoundly impacted how blockchain networks stay secure. If you’re wondering how PoS evolved and what that means for network security, the short answer is: it moved from being a simpler alternative to Proof-of-Work (PoW) to a sophisticated system with multiple layers of defense, making blockchains more energy-efficient and, in many ways, more resilient.
For a long time, Proof-of-Work (PoW) was the undisputed king of blockchain consensus. Think of Bitcoin – it uses an immense amount of electricity to solve complex puzzles, ensuring that transactions are validated and the network remains secure. While effective, this approach has significant drawbacks, most notably its environmental impact and the potential for centralization due to the high cost of specialized mining hardware.
The Energy Drain of PoW
The core issue with PoW is its inherent energy consumption. Every new block added to the chain requires a significant computational effort. This process is designed to be difficult, making it uneconomical for a single entity to control the majority of the network’s hashing power.
However, “uneconomical” still translates to a lot of wasted energy, often compared to the energy consumption of entire countries.
The Centralization Concern
While PoW aims for decentralization, the reality is that large mining pools and individuals with access to cheaper electricity and specialized hardware (ASICs) tend to dominate. This creates a risk of centralization, where a few powerful entities could potentially collude or influence the network.
Enter Proof-of-Stake
Proof-of-Stake emerged as a direct response to these challenges. Instead of relying on computational power, PoS networks select validators based on the amount of cryptocurrency they “stake” or hold. The more coins a validator stakes, the higher their chance of being chosen to validate new blocks and earn rewards. This fundamental shift aimed to address the energy and centralization issues plaguing PoW.
In exploring the advancements in blockchain technology, the article on Proof of Stake Evolution and Network Security highlights the significance of consensus mechanisms in enhancing network reliability. For a deeper understanding of how software solutions can optimize operational efficiency in various sectors, including blockchain, you can refer to this comprehensive guide on the best software for NDIS providers, which discusses innovative tools that can support service delivery and management. For more information, visit this link.
Key Takeaways
- Clear communication is essential for effective teamwork
- Active listening is crucial for understanding team members’ perspectives
- Setting clear goals and expectations helps to keep the team focused
- Regular feedback and open communication can help address any issues early on
- Celebrating achievements and milestones can boost team morale and motivation
Early PoS Models: Simplicity and Vulnerabilities
The initial iterations of PoS were, by necessity, simpler. The goal was to prove the concept and offer an alternative. While ingenious, these early designs also laid bare certain potential attack vectors that subsequent evolutions had to address.
“Nothing at Stake” Problem
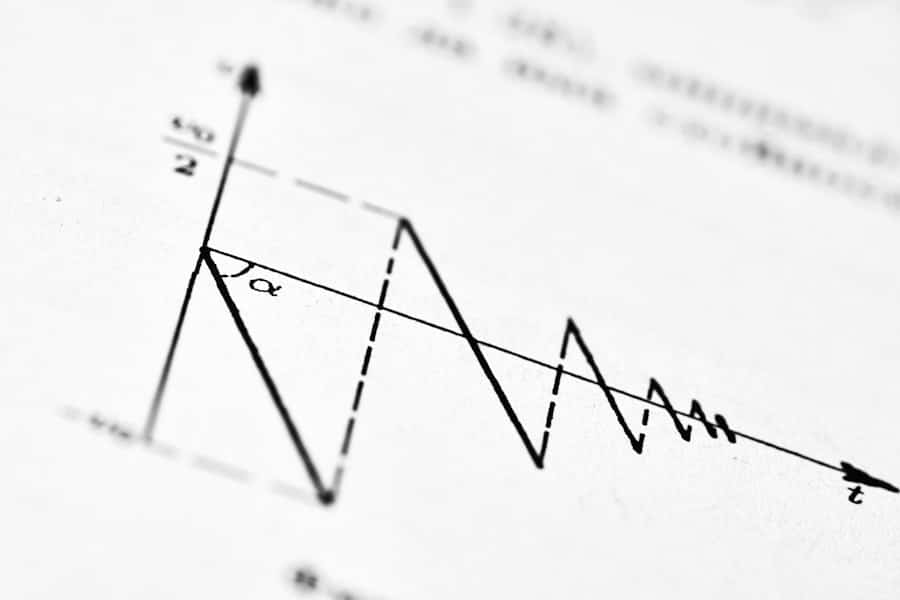
One of the most talked-about vulnerabilities in early PoS was the “Nothing at Stake” problem. In a PoW system, if a miner decides to mine on multiple chains simultaneously, they are essentially splitting their limited computational resources, making it less likely they’ll succeed on any single chain. In a naive PoS implementation, a validator could stake their coins and vote on multiple forks of the blockchain without any real cost. If a fork succeeded, they’d get rewards from that chain, and if it failed, they lost nothing significant since their stake remained intact. This could incentivize validators to support competing chains, making consensus formation difficult and potentially leading to instability.
Long-Range Attacks
Another concern was the “Long-Range Attack.” In this scenario, an attacker could acquire a large number of coins from an older block (potentially from when the coin was relatively cheap and easy to obtain) and then try to create an alternative, longer chain from that early point. Since the attacker would have a significant stake from the past, they could potentially rewrite history. This attack is less feasible in PoW due to the cumulative cost of redoing all the work.
Epoch-Based Staking
To mitigate some of these issues, early PoS systems often employed epoch-based staking. This meant that validators would commit their stake for a specific period (an epoch). If they misbehaved during that epoch, their stake could be slashed (partially or fully confiscated). This introduced a financial penalty, making misbehavior more costly than in a truly “nothing at stake” scenario.
The Evolution: Sophistication in Consensus Mechanisms
The initial challenges spurred significant research and development in PoS. Blockchain developers realized that simply replacing computational power with staking wasn’t enough. A more robust and nuanced approach was needed to ensure both security and true decentralization.
This led to the development of more sophisticated consensus mechanisms within the PoS framework.
Delegated Proof-of-Stake (DPoS)
Delegated Proof-of-Stake is a notable evolution. Instead of every coin holder having a chance to validate, token holders vote for a limited number of “delegates” or “witnesses.” These elected delegates are then responsible for validating transactions and producing blocks.
Pros of DPoS:
- Higher Transaction Speeds: With a smaller, elected set of validators, block production can be much faster.
- Increased Efficiency: The consensus process is streamlined.
Cons of DPoS:
- Potential for Centralization: The elected delegates can become a powerful group, and if voting power is concentrated, it can lead to issues.
- Voter Apathy: If token holders don’t actively participate in voting, the system can become less representative.
Tendermint Core and Byzantine Fault Tolerance (BFT)
Many modern PoS blockchains incorporate BFT consensus algorithms, and Tendermint Core is a prominent example. BFT algorithms are designed to achieve consensus even if a certain number of honest validators are offline or malicious (within defined limits, typically less than one-third).
Tendermint combines a Proof-of-Stake mechanism with a BFT consensus engine.
How Tendermint Works (Simplified):
Validators propose blocks in rounds. They vote on proposals, and if a supermajority agrees, the block is finalized. The staking mechanism determines who the validators are.
Benefits of BFT in PoS:
- Stronger Finality: Transactions are considered irreversible once confirmed, unlike the probabilistic finality in some PoW systems.
- Robustness against Network Issues: BFT can tolerate a higher degree of network disruption.
Hybrid PoS/PoW Models
Some projects have experimented with hybrid models, attempting to leverage the benefits of both PoW and PoS.
For instance, a network might use PoW for initial block production and PoS for finalization or to add an extra layer of security. However, these models can be complex to implement and manage effectively, and the trend has largely leaned towards purer PoS implementations.
Enhancing Security: Slashing and Penalties
A cornerstone of modern PoS security lies in its ability to punish malicious behavior. Unlike PoW, where the cost of an attack is primarily economic (electricity, hardware), PoS introduces direct financial penalties for validators who act against the network’s interests. This is often referred to as “slashing.”
The Mechanics of Slashing
Slashing occurs when a validator is caught engaging in dishonest or harmful activities. Common triggers for slashing include:
- Double Signing: Attempting to validate two different blocks at the same height. This directly violates the single source of truth principle of a blockchain.
- Liveness Failures: Repeatedly going offline and failing to participate in block production for extended periods without proper justification. This can disrupt consensus.
- Attacking the Network: Actively trying to forge transactions, censor valid transactions, or participate in other malicious activities.
The Economic Incentive for Good Behavior
Slashing is a powerful deterrent. If a validator’s stake is partially or fully confiscated, they incur a direct financial loss beyond just the opportunity cost of not earning rewards. This creates a strong economic incentive for validators to act honestly and diligently. The system effectively “puts their money where their mouth is.”
Diversification of Validators
The risk of slashing also encourages validators to be more careful and to run their infrastructure reliably. This promotes better operational practices among validators. Furthermore, a healthy distribution of staked cryptocurrency among many independent validators makes it harder for any single entity or group to collude and execute an attack, as the impact of slashing would be spread, and the cost of acquiring enough stake to control a significant portion of the network would be prohibitive.
In exploring the advancements in blockchain technology, the evolution of Proof of Stake and its implications for network security is a critical topic. A related article that delves into the nuances of this subject can be found at this link, where it discusses how these mechanisms not only enhance security but also promote energy efficiency compared to traditional Proof of Work systems. Understanding these developments is essential for anyone interested in the future of decentralized networks.
The Role of Validators and Stakers
| Metrics | Proof of Stake Evolution | Network Security |
|---|---|---|
| Number of Validators | Increasing | Higher number enhances security |
| Staking Participation | Growing | Higher participation increases security |
| Decentralization | Improving | More decentralized networks are more secure |
| Security Mechanisms | Enhancing | Continuous improvement in security protocols |
Understanding how PoS networks function requires appreciating the distinct but interconnected roles of validators and stakers. These groups are the backbone of the network’s security and operation.
Validators: The Active Participants
Validators are the entities responsible for proposing and validating new blocks in a PoS network. They typically run specialized software and maintain reliable network connections. To become a validator, an individual or entity needs to stake a significant amount of the network’s native cryptocurrency. The higher the stake, generally the higher the probability of being selected to propose a block.
Responsibilities of Validators:
- Proposing New Blocks: Creating and broadcasting new blocks of transactions to the network.
- Validating Transactions: Verifying the legitimacy of transactions within a block.
- Participating in Consensus: Voting on proposed blocks and reaching agreement with other validators.
- Maintaining Network Uptime: Ensuring their validator node is consistently online and operational.
Stakers: The Passive Supporters
Stakers are cryptocurrency holders who choose to lock up their coins in a PoS network to earn rewards. They might not have the technical expertise or desire to run a validator node themselves. Instead, they can delegate their stake to an existing validator.
Benefits for Stakers:
- Earning Passive Income: Stakers earn rewards in the form of newly minted coins or transaction fees.
- Contributing to Network Security: By staking, they increase the overall security and decentralization of the network.
Delegation and its Implications:
Delegation is a key feature that allows for greater participation in PoS. Stakers can choose validators they trust, and in return, the validator offers a portion of their earned rewards. This creates a symbiotic relationship: stakers gain yield while validators gain more stake, thus increasing their chances of being selected and earning more. However, it’s crucial for stakers to research validators to ensure they are reputable and have a good track record.
Future Directions and Innovations in PoS Security
The evolution of Proof-of-Stake is far from over. Researchers and developers are continuously exploring new ways to enhance its security, scalability, and decentralization, pushing the boundaries of what’s possible in blockchain technology.
Sharding and Layer-2 Solutions
While not strictly a PoS security feature itself, sharding and Layer-2 solutions are innovations that will indirectly bolster the security of PoS networks by distributing network load and enabling more transactions. Sharding could allow for parallel processing of transactions across different “shards” of the blockchain, reducing the burden on individual validators. Layer-2 solutions, like state channels and rollups, process transactions off-chain, settling them on the main PoS chain, which can improve transaction throughput while still inheriting the security of the underlying consensus mechanism.
Verifiable Delay Functions (VDFs)
VDFs are cryptographic tools that can be used to introduce a verifiable delay in computation. In the context of PoS, VDFs can be employed to ensure that block proposers are chosen in a truly random and unpredictable manner, making it harder for attackers to anticipate or influence the selection process. This can add an extra layer of randomness and fairness to validator selection.
Advanced Cryptographic Techniques
Ongoing research into advanced cryptographic techniques, such as zero-knowledge proofs (ZKPs) and secure multi-party computation (MPC), could also play a role in future PoS security. ZKPs might enable validators to prove the validity of transactions without revealing sensitive information, enhancing privacy and potentially reducing the attack surface. MPC could allow for more secure and distributed key management among validators.
Decentralized Governance and Protocol Upgrades
Ultimately, the long-term security of any PoS network will depend on its ability to adapt and evolve. Decentralized governance mechanisms, where token holders have a say in protocol upgrades and parameter changes, are becoming increasingly important. This allows the network to respond to new threats and implement improvements in a community-driven manner, fostering a more resilient and adaptive security posture.
The ability to collectively decide on and implement security patches or upgrades is a crucial aspect of future-proofing PoS networks.
FAQs
What is Proof of Stake (PoS) and how does it differ from Proof of Work (PoW)?
Proof of Stake (PoS) is a consensus algorithm used in blockchain networks to validate and create new blocks. It differs from Proof of Work (PoW) in that PoS relies on validators who hold a stake in the network to create and validate new blocks, while PoW relies on miners who solve complex mathematical puzzles to validate transactions and create new blocks.
How does Proof of Stake contribute to network security?
Proof of Stake contributes to network security by requiring validators to hold a stake in the network, which serves as an economic incentive for them to act honestly. Validators who attempt to validate fraudulent transactions or create invalid blocks risk losing their stake, thus providing a strong deterrent against malicious behavior.
What are some examples of blockchain networks that use Proof of Stake?
Some examples of blockchain networks that use Proof of Stake include Ethereum 2.0, Cardano, Tezos, and Cosmos. These networks have implemented or are in the process of transitioning to a PoS consensus algorithm to improve scalability, energy efficiency, and network security.
What are the potential drawbacks of Proof of Stake?
One potential drawback of Proof of Stake is the “nothing at stake” problem, where validators have little to lose by supporting multiple conflicting chains, potentially leading to network instability. Additionally, PoS may lead to centralization if a small number of validators hold a significant portion of the network’s stake.
How is Proof of Stake evolving to address its limitations and improve network security?
Proof of Stake is evolving through the implementation of mechanisms such as slashing penalties, which penalize validators for dishonest behavior, and randomization techniques to select validators and prevent centralization. Additionally, ongoing research and development aim to address the “nothing at stake” problem and further enhance network security.

