Here’s an article on how to make security awareness training more effective, written in a factual, Wikipedia-style:
Security awareness training aims to educate individuals within an organization about potential security threats and best practices to mitigate them. Effective training is crucial because human error remains a significant vector for cyberattacks. While many organizations implement security awareness programs, their effectiveness can vary widely. This article explores strategies to enhance the impact and retention of security awareness training.
Successful security awareness training begins with a deep understanding of the audience. Employees are not a monolithic group; they possess different levels of technical proficiency, varying job responsibilities, and distinct learning styles. A one-size-fits-all approach is often akin to casting a wide net hoping for a specific fish – inefficient and prone to missing the mark. Instead, training should be tailored to resonate with the individual’s daily work and their personal interactions with technology.
Identifying the Target Audience
The first step in crafting effective training is to accurately identify who needs to be trained and their specific roles.
Differentiated Training Tracks
Consider creating distinct training modules for different departments or job functions. For example, finance departments may require specialized training on handling sensitive financial data and recognizing phishing attempts targeting financial transactions. IT staff might need more in-depth knowledge of network security protocols, while customer-facing roles could focus on social engineering tactics aimed at eliciting personal information. This segmentation ensures that the material is relevant and directly addresses the unique risks each group faces.
Assessing Risk Exposure
Analyze the specific security risks that each employee group is exposed to. This requires a risk assessment that goes beyond generic threats. If a particular team frequently handles customer personally identifiable information (PII), their training should heavily emphasize data privacy regulations and secure handling procedures. If another team regularly interacts with third-party vendors, training on vendor risk management and secure data exchange becomes paramount.
Understanding Learning Styles and Preferences
Recognize that individuals learn in different ways. Some absorb information best through visual aids, others through auditory explanations, and some prefer hands-on, interactive exercises.
Visual Learning Aids
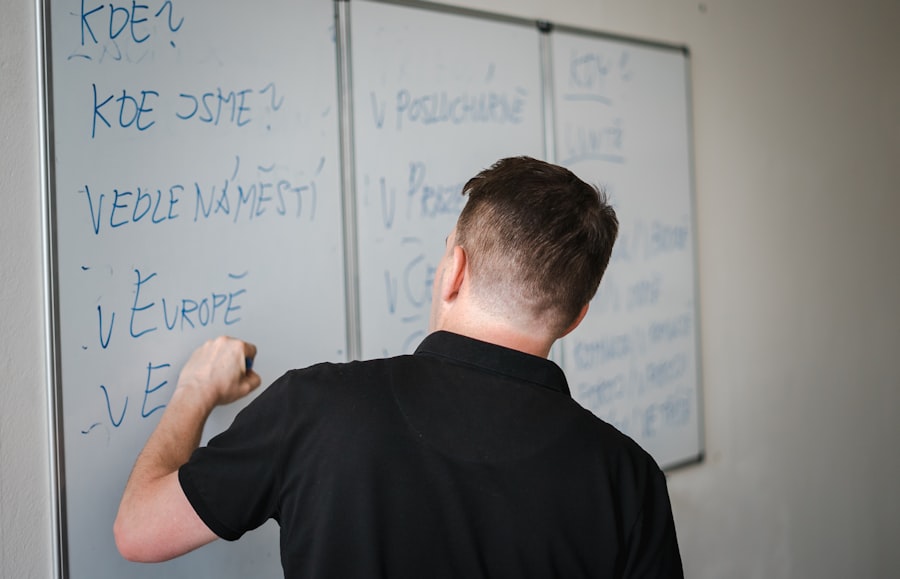
Incorporate a variety of visual elements. Infographics, diagrams illustrating complex concepts, and short, engaging videos can significantly enhance comprehension and retention. For instance, a visual flowchart demonstrating the steps of reporting a suspicious email can be more effective than a lengthy textual explanation.
Auditory Learning Components
For those who prefer auditory learning, consider incorporating podcasts, webinars with clear spoken explanations, and even role-playing scenarios that can be listened to and discussed.
Kinesthetic and Interactive Learning
Hands-on activities are vital for solidifying knowledge. This can include interactive quizzes, simulations of phishing attacks, and practical exercises in identifying malicious content. Learning by doing, rather than just by observing, leaves a more lasting impression.
In exploring the ways to enhance the effectiveness of security awareness training, it is essential to consider the role of technology in our daily lives. A related article that delves into the intersection of technology and user engagement is found at this link: The Best Smartwatch Apps of 2023. This article highlights innovative applications that can help individuals stay informed and vigilant about security threats, thereby complementing the objectives of security awareness programs. By integrating such tools into training initiatives, organizations can foster a more proactive security culture among their employees.
Content Design and Delivery
The substance of security awareness training, as well as how it is delivered, are critical determinants of its effectiveness. Simply presenting a long list of rules or warnings is unlikely to foster genuine understanding or behavioral change. The content needs to be engaging, memorable, and directly applicable to real-world scenarios.
Making Content Relevant and Engaging
Security threats are constantly evolving, and training content must keep pace to remain relevant. Stale information is like yesterday’s newspaper – uninteresting and irrelevant.
Scenario-Based Learning
Instead of abstract warnings, present training through realistic scenarios that employees are likely to encounter. For example, instead of stating “be careful of phishing emails,” present a simulated phishing email and ask the employee to identify its suspicious elements and explain the potential consequences of clicking a malicious link. This active engagement fosters critical thinking.
Storytelling and Real-World Examples
Human beings are naturally drawn to stories. Share anonymized examples of past security incidents within the organization or well-known public breaches, highlighting the human element that led to the compromise. This makes the threats tangible and emphasizes the importance of individual vigilance.
Gamification and Micro-Learning
Break down complex security concepts into smaller, digestible modules, often referred to as micro-learning. Incorporate game-like elements such as points, badges, and leaderboards to motivate participation and reinforce learning. This approach can transform what might otherwise be a tedious task into an engaging challenge.
Choosing the Right Delivery Methods
The platform and method of delivery can significantly influence how well the message is received and retained. A rigid, infrequent lecture approach is rarely optimal.
Regular and Short Training Sessions
Short, frequent training sessions are generally more effective than a single, lengthy annual training. This principle of spaced repetition aids memory retention and keeps security top-of-mind. Think of it as regular check-ups for your digital health rather than one major surgery every year.
Blended Learning Approaches
Combine various delivery methods to cater to different learning styles and preferences. This could include a mix of online modules, in-person workshops, interactive simulations, and even informal Q&A sessions with security personnel.
Just-In-Time Training
Provide security information and reminders when and where they are most needed. For example, if an employee is about to access a sensitive system or download a potentially risky file, a brief, context-specific security prompt can be highly effective.
Reinforcement and Measurement

Effective security awareness training is not a one-time event. It requires ongoing reinforcement and a system to measure its impact to identify areas for improvement. Without these elements, the training can quickly fade into the background noise of daily operations.
Continuous Reinforcement Strategies
The initial training is just the seed; reinforcement is the ongoing watering and sunlight that allows it to grow. Without consistent nurturing, the knowledge can wither.
Phishing Simulations
Regularly conduct simulated phishing campaigns to test employee awareness in a controlled environment. The immediate feedback provided to those who fall for the simulation, coupled with remedial training, is a powerful learning tool. This is akin to a fire drill – it’s best to practice when the alarm isn’t real.
Security Newsletters and Alerts
Distribute regular newsletters or alerts that highlight current threats, recent security incidents (anonymized), and provide practical tips. This keeps security relevant and educates employees on evolving risks in a timely manner.
Security Reminders and Posters
Place subtle, informative reminders and posters in common areas or digital workspaces. These act as visual cues that reinforce key security messages without being intrusive.
Measuring Training Effectiveness
To understand if the training is working, you need to measure its outcomes. Relying solely on completion rates provides a false sense of security; it tells you people showed up, not that they learned or changed their behavior.
Tracking Key Performance Indicators (KPIs)
Identify relevant KPIs such as a reduction in reported security incidents attributable to human error, a decrease in successful phishing clicks, and an increase in reported suspicious activities by employees.
Post-Training Assessments and Surveys
Administer follow-up quizzes or surveys to assess knowledge retention and identify areas where employees still struggle. These assessments should ideally be conducted weeks or months after the initial training to gauge long-term recall.
Behavioral Observation and Feedback
Where feasible, observe employee behavior related to security practices. This can be done through audits or by encouraging a culture where employees feel comfortable providing feedback on security procedures.
Cultivating a Security-Conscious Culture
Ultimately, the goal of security awareness training is to foster a culture where security is not an afterthought but an integral part of everyone’s role. This transforms individuals from potential liabilities into active defenders.
Leadership Buy-In and Role Modeling
Senior leadership must champion security awareness initiatives for them to be truly effective. When leaders prioritize and participate in security training, it signals its importance throughout the organization.
Visible Support from Management
When executives openly discuss the importance of security, attend training sessions, and reinforce security messages, it sets a powerful precedent. Their commitment acts as a beacon, guiding the entire organization towards a more secure posture.
Integrating Security into Performance Reviews
Consider integrating adherence to security policies and practices into performance evaluations. This reinforces that security is a measurable aspect of an employee’s contribution.
Empowering Employees as Security Advocates
Encourage employees to be proactive in identifying and reporting potential security risks. Create channels for them to easily report concerns without fear of reprisal.
Anonymous Reporting Mechanisms
Provide secure and anonymous channels for employees to report security vulnerabilities or concerns. This allows individuals to speak up without worrying about personal consequences, acting as an early warning system.
Recognizing and Rewarding Security Vigilance
Acknowledge and reward employees who demonstrate exceptional vigilance or contribute to improving the organization’s security posture. This positive reinforcement further strengthens the desired behaviors.
To enhance the effectiveness of security awareness training, it is crucial to consider various factors that influence learning outcomes. One insightful article discusses the best laptops for teachers in 2023, which can be particularly relevant for educators looking to implement engaging training sessions. By utilizing the right technology, trainers can create interactive and immersive experiences that resonate with participants. For more information on suitable devices that can aid in this process, you can check out the article on the best laptops for teachers here.
Addressing Emerging Threats and Advanced Concepts
| Metric | Description | Example Data | Impact on Effectiveness |
|---|---|---|---|
| Phishing Simulation Click Rate | Percentage of employees who click on simulated phishing emails | Initial: 25% After Training: 8% |
Lower click rates indicate improved awareness and training effectiveness |
| Training Completion Rate | Percentage of employees who complete the security awareness training | 95% | Higher completion rates ensure wider knowledge dissemination |
| Knowledge Retention Score | Average score on post-training quizzes or assessments | Pre-training: 60% Post-training: 85% |
Higher scores reflect better understanding and retention |
| Incident Reporting Rate | Number of security incidents reported by employees | Before Training: 5/month After Training: 15/month |
Increased reporting shows heightened vigilance and proactive behavior |
| Training Frequency | Number of training sessions per year | Quarterly (4 times/year) | Regular sessions help reinforce knowledge and update on new threats |
| Engagement Rate | Percentage of employees actively participating in interactive training elements | 70% | Higher engagement correlates with better learning outcomes |
| Behavioral Change Rate | Percentage of employees adopting secure behaviors post-training | 65% | Indicates practical application of training in daily work |
The threat landscape is a moving target, constantly shifting with new technologies and evolving attacker tactics. Security awareness training must evolve accordingly to address these dynamic challenges.
Keeping Pace with New Threats
The cybersecurity world is a rapidly flowing river, and what was considered safe yesterday might be a hazard today. Training needs to be as agile as the threats it seeks to counter.
Dynamic Threat Intelligence Integration
Incorporate real-time threat intelligence into training materials. This ensures that employees are educated on the very latest phishing techniques, malware strains, and social engineering tactics being employed by attackers.
Regular Content Updates
Schedule regular reviews and updates of training content to reflect emerging threats and changes in organizational policies or technologies. A static training program will inevitably become outdated.
Introducing Advanced Security Concepts
Beyond basic best practices, employees may benefit from understanding more complex security concepts relevant to their roles. This can empower them to make more informed decisions and contribute to a stronger overall security posture.
Understanding the Concepts of Zero Trust
Introduce the principles of Zero Trust architecture, explaining its implications for access control and data protection, even for internal users. This shifts the paradigm from implicit trust to explicit verification.
Recognizing Advanced Persistent Threats (APTs)
Educate employees on the characteristics of APTs, which are often sophisticated, long-term attacks designed to infiltrate systems undetected. Understanding these advanced threats can help foster a more discerning approach to unusual system behavior.
Data Loss Prevention (DLP) and Its Role
Explain the role of DLP solutions and how individual actions can impact their effectiveness. This can include awareness of data exfiltration attempts and the importance of adhering to data handling policies.
By implementing these strategies, organizations can move beyond perfunctory security awareness training and cultivate a truly security-conscious workforce, transforming individuals from passive recipients of information into active participants in safeguarding the organization’s digital assets.
FAQs
What is security awareness training?
Security awareness training is an educational program designed to teach employees and users about cybersecurity best practices, potential threats, and how to recognize and respond to security risks to protect organizational data and systems.
Why is security awareness training important?
It helps reduce the risk of security breaches caused by human error by increasing employees’ knowledge of cyber threats such as phishing, social engineering, and malware, thereby strengthening an organization’s overall security posture.
How can security awareness training be made more effective?
Effectiveness can be improved by using engaging, interactive content, providing real-world examples, conducting regular training sessions, tailoring the material to specific roles, and reinforcing learning through simulated phishing tests and ongoing communication.
How often should security awareness training be conducted?
Training should be conducted regularly, typically at least annually, with additional refresher sessions or updates whenever new threats emerge or organizational policies change to ensure continuous awareness and preparedness.
What role do simulated phishing exercises play in security awareness training?
Simulated phishing exercises provide practical, hands-on experience by mimicking real phishing attacks, helping employees recognize suspicious emails and behaviors, which reinforces training concepts and improves their ability to respond appropriately to actual threats.

